Kaya Platform Overview:
Enterprise Intelligence Execution
Run AI Inside Real Operations
Deterministically. Securely. At scale.
KAYA brings AI from experimentation into production-grade operations.
Where most AI initiatives fail due to weak execution control and disconnected services, KAYA enforces enterprise-grade discipline—making intelligence predictable, auditable, and aligned to real business outcomes.
- Architecture
Modular, cloud-agnostic design
- Workspaces
Connected enterprise surfaces
- Intelligent Flows
Core execution units
- Governance
Embedded controls
- Security
Identity-first execution
Architecture
Built for Enterprise Scale
KAYA is built on a modular, cloud-agnostic architecture designed for high-scale, high-trust enterprise environments. The platform intentionally separates execution, control, and integration concerns, enabling reliable scaling without loss of governance or consistency.
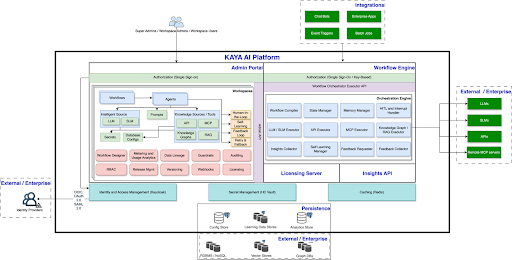
Key Architectural Principles
- Proprietary Deterministic Execution
Predictable execution paths with audit-ready outcomes across AI, systems, and human decisions.
- Stateless Compute, Persistent Intelligence
Scalable execution with persistent state, context, and execution history.
- Policy-Enforced Control Plane
Control, audit, Authoring and monitor AI execution across your enterprise value ecosystem.
- Governed Agent-to-Agent Communication
A secure, interoperable A2A layer with policy-controlled context exchange.
- Context as a Governed Asset
Explicit, scoped, validated, and fully traceable context propagation across agents and systems.
- Execution-Aware Feedback Loops
Controlled learning and continuous improvement without breaking determinism or governance.
- Enterprise-Grade Resilience
Built-in recovery, scalability, high availability, and fault tolerance for real-world operations.
- Auditability by Construction
Execution is inherently traceable, enabling compliance, risk reduction, and end-to-end audit readiness.
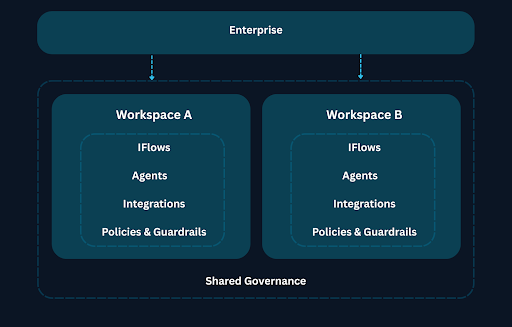
Workspace
Enabling the Connected Enterprise
A governed operating surface where people, systems, APIs, agents, and intelligent flows come together.
Workspaces define execution boundaries across teams, environments, and business domains. They enable decentralized execution with centralized control and enterprise reusability.
This is how enterprises operate AI without fragmentation.
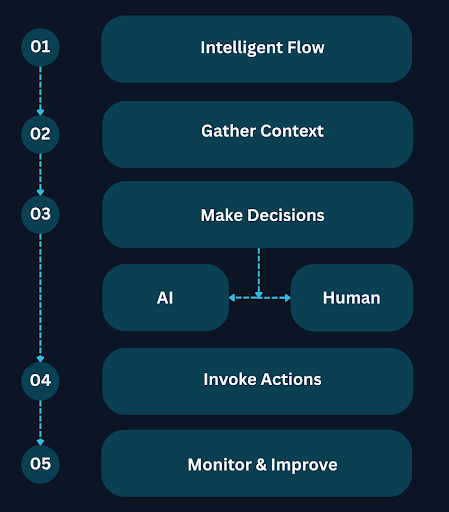
Intelligent Flows (iFlows)
The Core Execution Unit
Intelligent Flows are the core execution unit of the KAYA platform.
They coordinate AI agents, enterprise systems, data, and human decisions within governed execution graphs.
Designed for real operations, Intelligent Flows handle uncertainty, exceptions, and governance as part of execution — not as afterthoughts.
Governance & Controls
Governance Embedded into Execution
Intelligent Flows are authored with built-in controls, ensuring humans remain in control of AI behavior throughout execution—not through manual oversight, but through enforceable execution constraints.
Policy enforcement, execution-level explainability, human approval gates, and immutable audit trails ensure every action is compliant, traceable, and accountable.
End-to-End Data Lineage
Governance extends beyond decisions to data itself
Crucially, governance in KAYA extends beyond decisions and actions to data itself. Every execution captures end-to-end data lineage, recording the complete journey of information through your enterprise systems.
- Which data sources were accessed
- How data and context were transformed or enriched
- Where data flowed across agents, systems, and decisions
Complete Verifiable Record
This allows enterprises to trace outcomes not only to who approved what, but also to which data influenced each decision and how it moved through execution. Governance, accountability, and data lineage are inseparable—providing a complete, verifiable record of how AI operates inside the enterprise.
Security
Identity-First Execution Model
KAYA follows an identity-first execution model where every action is authenticated, authorized, and attributable.
Fine-grained access controls, least-privilege execution, secure credential management, tenant isolation, and end-to-end encryption are enforced across the platform.
- Identity-First Execution
- Role-Based Access Control
- Secure Credential Management
- Tenant Isolation
- End-to-End Encryption
- SOC 2 & HIPAA Alignment
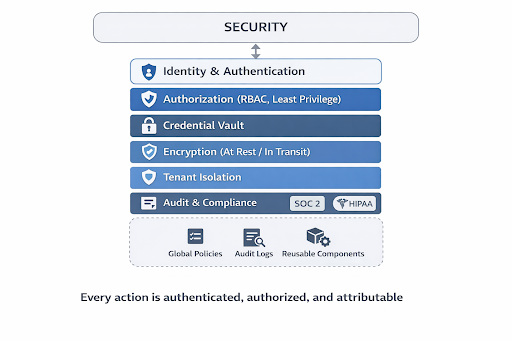
The platform aligns with enterprise security and compliance standards including SOC 2 and HIPAA and supports full execution auditability.

