Security — Identity-First, Execution-Aware by Design
Security in Kaya is not perimeter-based or bolted on through tooling.
It is intrinsic to how execution occurs.
Authenticated, Authorized, Attributable
Every action taken by the platform—human, agent, or system—is authenticated, authorized, and attributable. Security is enforced at the execution layer, where decisions turn into actions, rather than at the edges of the system.
Alignment with Enterprise Security and Compliance Standards
Kaya is built to align with enterprise security expectations and regulatory requirements. Security controls are enforced by execution, ensuring compliance is maintained continuously—not verified periodically.
- SOC 2 Type 2
- HIPAA
- ISO 27001
- Enterprise Controls
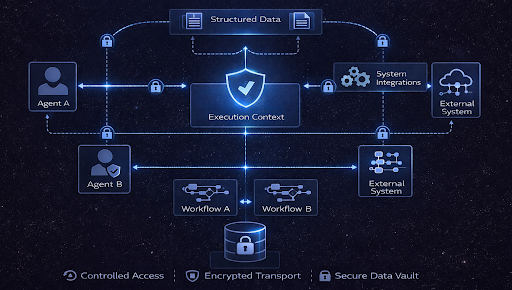
Fine-Grained Access and Least-Privilege Execution
Access in Kaya is enforced through fine-grained, role-based controls aligned to execution responsibilities.
Permissions are applied across:
- Workspaces
- Flows and execution stages
- Data access
- System integrations
Execution always operates under least-privilege principles. If an identity is not explicitly authorized to perform an action, execution does not proceed.

Secure Secrets and Credential Handling
Kaya never exposes credentials inside prompts, flows, or runtime logic.
Protected Assets
Sensitive assets are stored in secure, encrypted vaults and injected into execution only when explicitly authorized and required:
- API keys
- Tokens
- Certificates
- Environment secrets
Secret Properties
All secrets are:
- Encrypted at rest and in transit
- Scoped to workspaces and flows
- Fully auditable in terms of usage
Data Protection Across Execution
Security in Kaya extends to data in motion and data at rest.
The platform enforces:
- Controlled data access based on execution context
- Secure handling of structured and unstructured data
- Encrypted communication between agents, systems, and services
Data access is always governed by execution policy, ensuring sensitive information is only used where permitted and necessary.
Tenant and Environment Isolation
Kaya is designed for multi-tenant, multi-environment enterprise deployments.
- Tenants
- Environments
- DEV / QA / PROD
- Workspaces
- Execution Contexts
Strong isolation ensures that actions, data, and credentials never leak across organizational or environmental boundaries.
Security with Built-In Accountability
Every security-relevant event in Kaya is inherently traceable.
Traceable Events
- Access attempts
- Authorization decisions
- Credential usage
- System interactions
Enabling Capabilities
Security events are captured as part of execution records, not separate logs, enabling:
- Incident investigation
- Forensic analysis
- Compliance validation